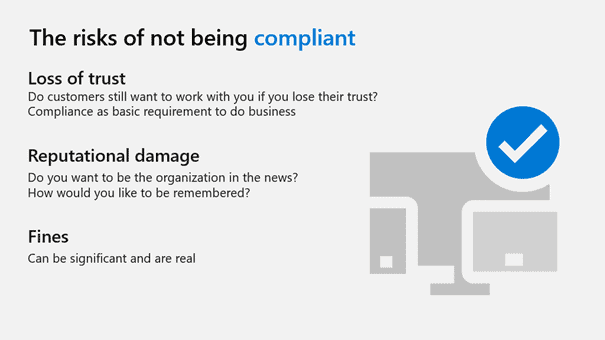
Hopefully, by now, your audience has a sense of the magnitude of the problem. The magnitude of that problem should also communicate that it is too large for you to manage with the resources you have. The implication is while you are aware of the problem and understand it. You simply don’t have the ability to solve it with the tools you have. But you’re not done yet. Next, you need to make this more than just IT’s a problem. You need to make it the organization’s problem. What are the risks of data loss or compromise? What’s the downside? Should it happen? What’s the worst possible outcome? This needs to be dramatic but not far-fetched. Your audience has seen enough news about breaches and the consequences to responsible organizations, so you shouldn’t have to try too hard. Real examples that could affect your organization are the way to go.